It's FOSS turns 14 tomorrow. Incidentally, my son turns 1 tomorrow as well. Two milestones the same day call for celebration, right?
But there is something important that I wanted to share with you and it relates to the future of It's FOSS.
The thing is that Google Search is gone. Not broken but gone. What replaces it is an AI that reads the web, summarizes it, and hands you the answer directly. No links. No clicks. No visits to the sites that actually wrote the content.
This is not a minor update. This is a structural shift in how the internet works.
For the past two decades, a quiet but fair deal powered the open web: you search, you click, we earn a little from ads, and we use that to keep writing. That deal is over. Google now takes our content, serves the answer, and the publisher gets nothing. Not even a visit.
Since the launch of ChatGPT, It's FOSS has already lost 80% of its Google search traffic. And it's alarming now.
I built It's FOSS because I love Linux and open-source software. Not to get rich. I built it because I wanted a place where people could learn Linux for free, stay informed, and feel part of a community that actually cares about what open-source software means. For years, that worked. Ad revenue kept the lights on. We kept creating informational content that helped Linux users all around the world.
That model is now broken, and no tweak to our content strategy will fix it. This is not an algorithm we can optimize around.
The big publishers will survive this. They have corporate backing, licensing deals, and investors to absorb the losses. We don't. What we have is you.
If It's FOSS has ever helped you, fixed a problem, taught you something new, saved you a frustrating hour, this is the moment to return the favor. You want us to continue for 14 more years, right?
Becoming a Plus member keeps this alive:
- The newsletter you're reading right now
- The tutorials, guides, and news on It's FOSS
- A small, independent voice in a world where content is increasingly written by non-humans for non-humans
To mark 14 years of It's FOSS (and my son's first birthday), I'm offering $30 off the lifetime membership this week. This one-time payment also solidifies the trust you have in It's FOSS and keeps us going in the age of AI slop.
Not in a position to subscribe? A one-time donation helps too. Every contribution, whatever the size, is a vote for keeping It's FOSS alive, keeping the open web alive.
I've spent years writing about open source because I believe software freedom matters, using a free operating system matters. I still do. But this freedom also needs people willing to sustain the communities that talk about it.
I'm asking you to be one of those people.
📰 News That Matter
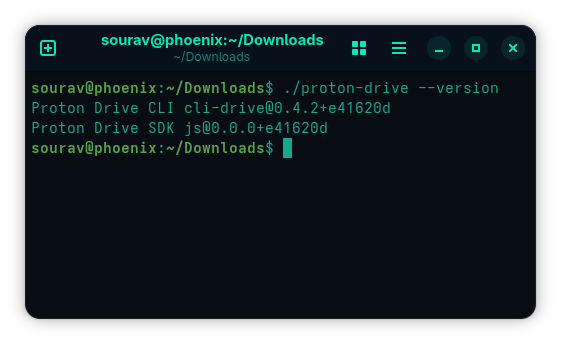
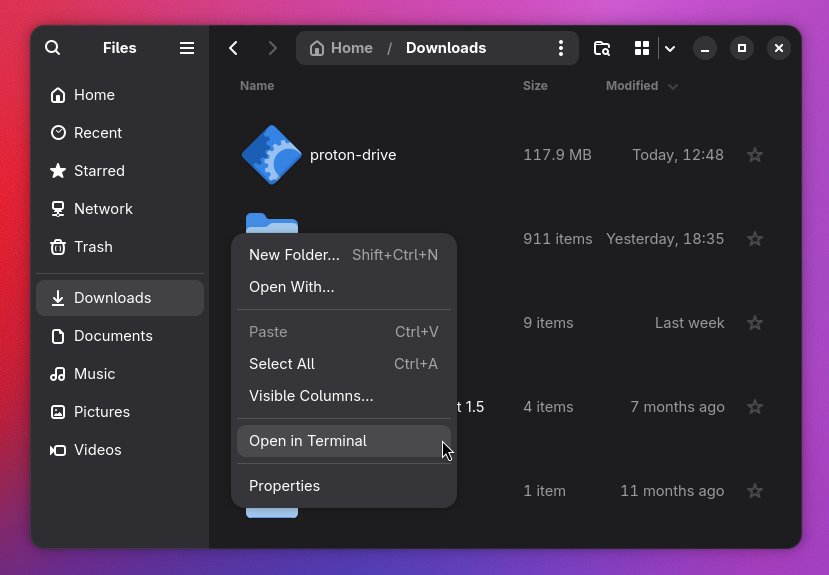
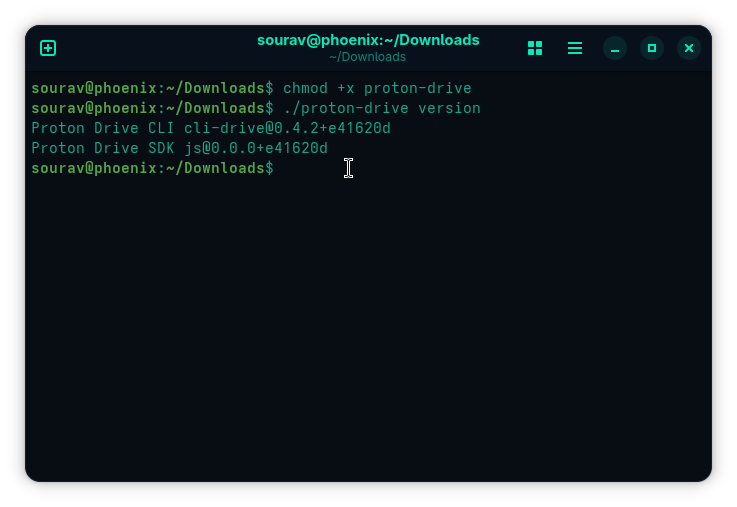
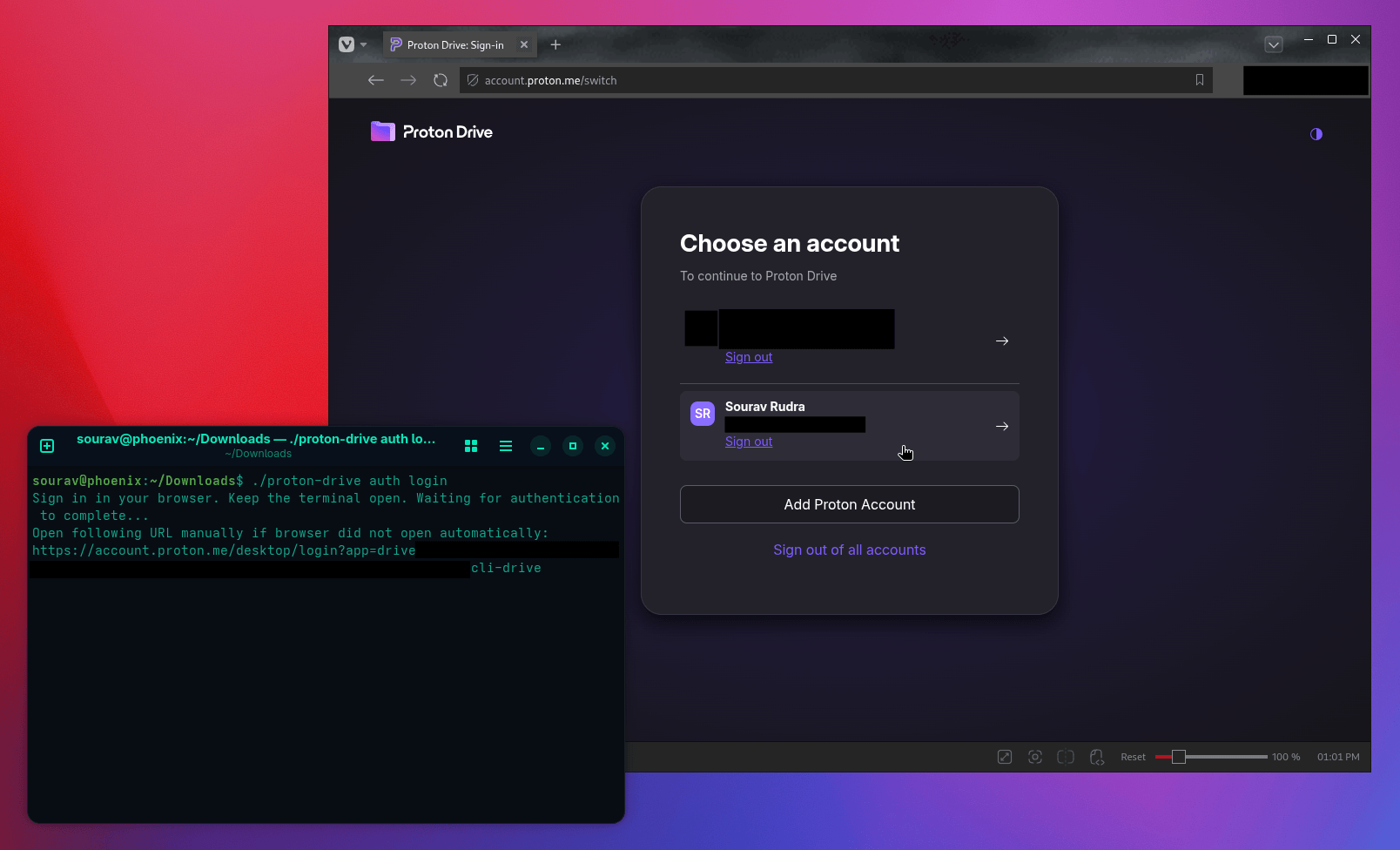
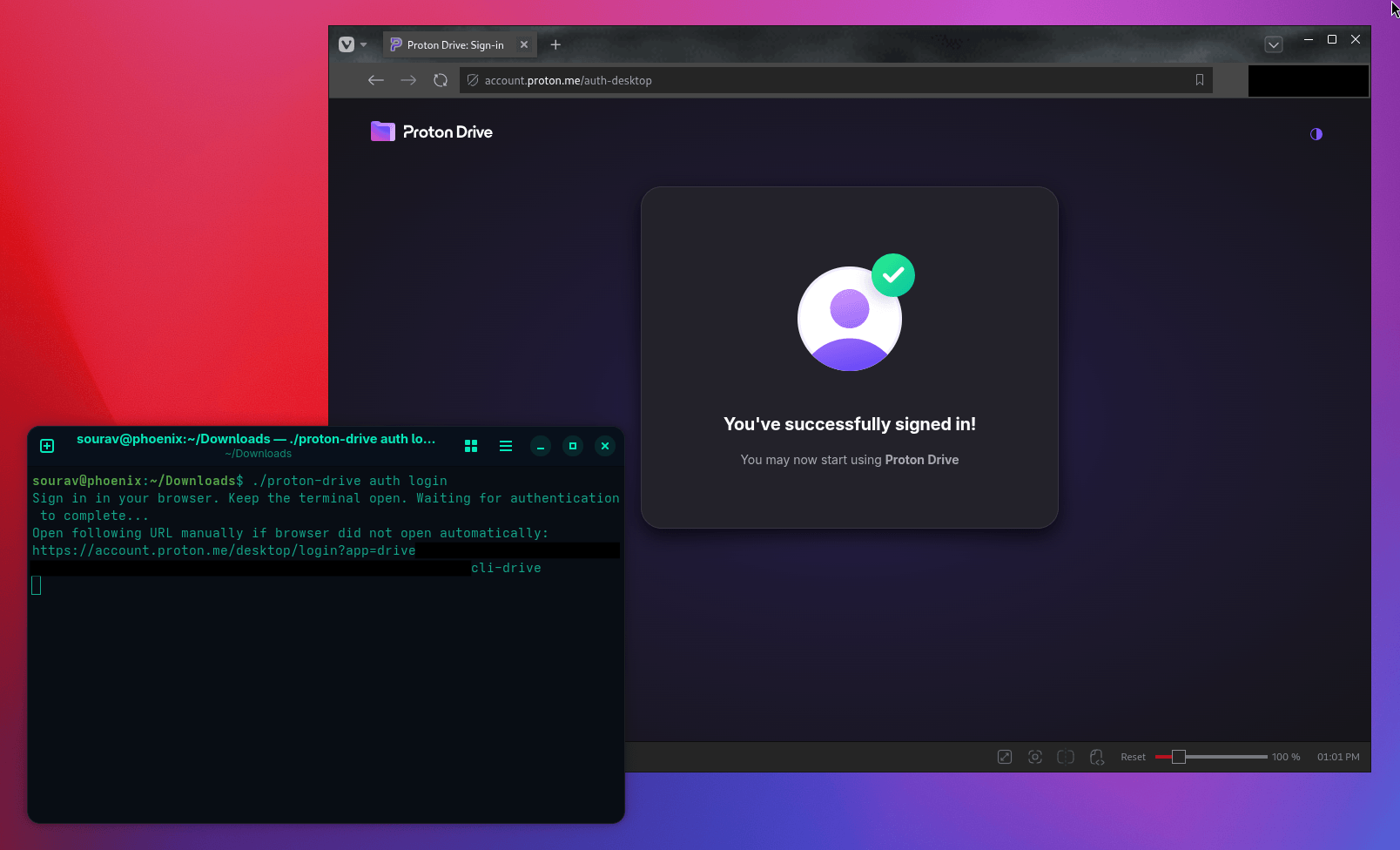
Proton has given us some back-to-back updates. There's an encryption overhaul that makes uploads up to 3x faster and downloads up to 2x faster, thanks to a cryptography rewrite. News on how a native GUI client for Linux is in the works, and an official CLI offering for Drive that works on Linux, Windows, and macOS.
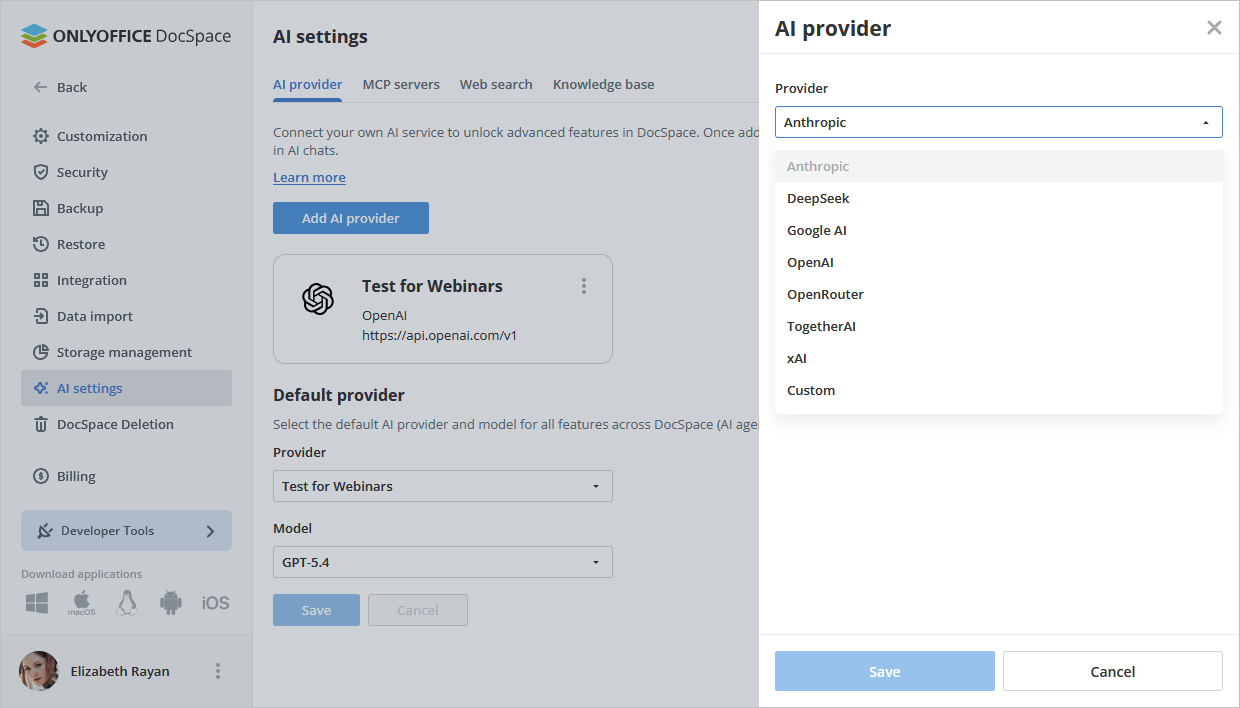
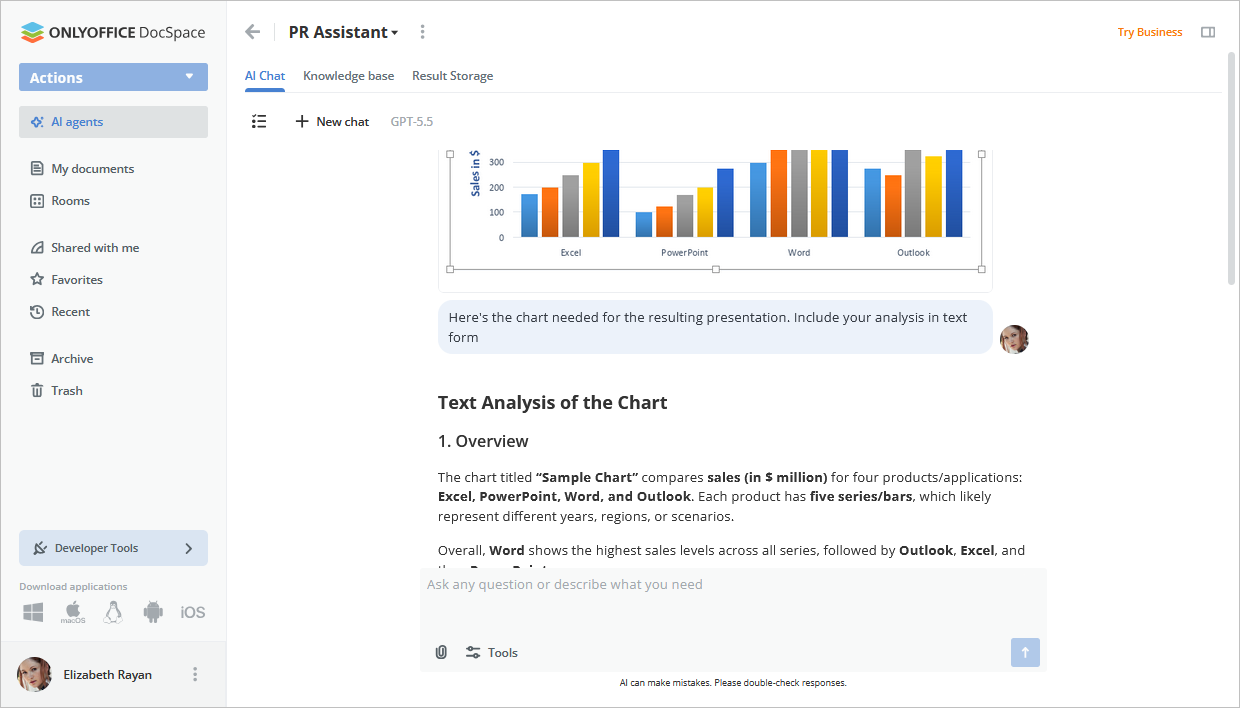
A lot has landed in the DocSpace 3.7 release. You get AI-generated files, DeepSeek, xAI and Google AI support, a complete rework of form filling rooms that now handle PDF creation, room tagging, bulk deletion, and new admin controls.
Similarly, Collabora have introduced CODE 26.04, possibly their biggest release yet. It includes AI assistance across all three editors, a reworked document comparison tool in Writer, per-user sheet views in Calc, 14 new spreadsheet functions, and a follow-me presentation mode in Impress. Yeah... AI everywhere.
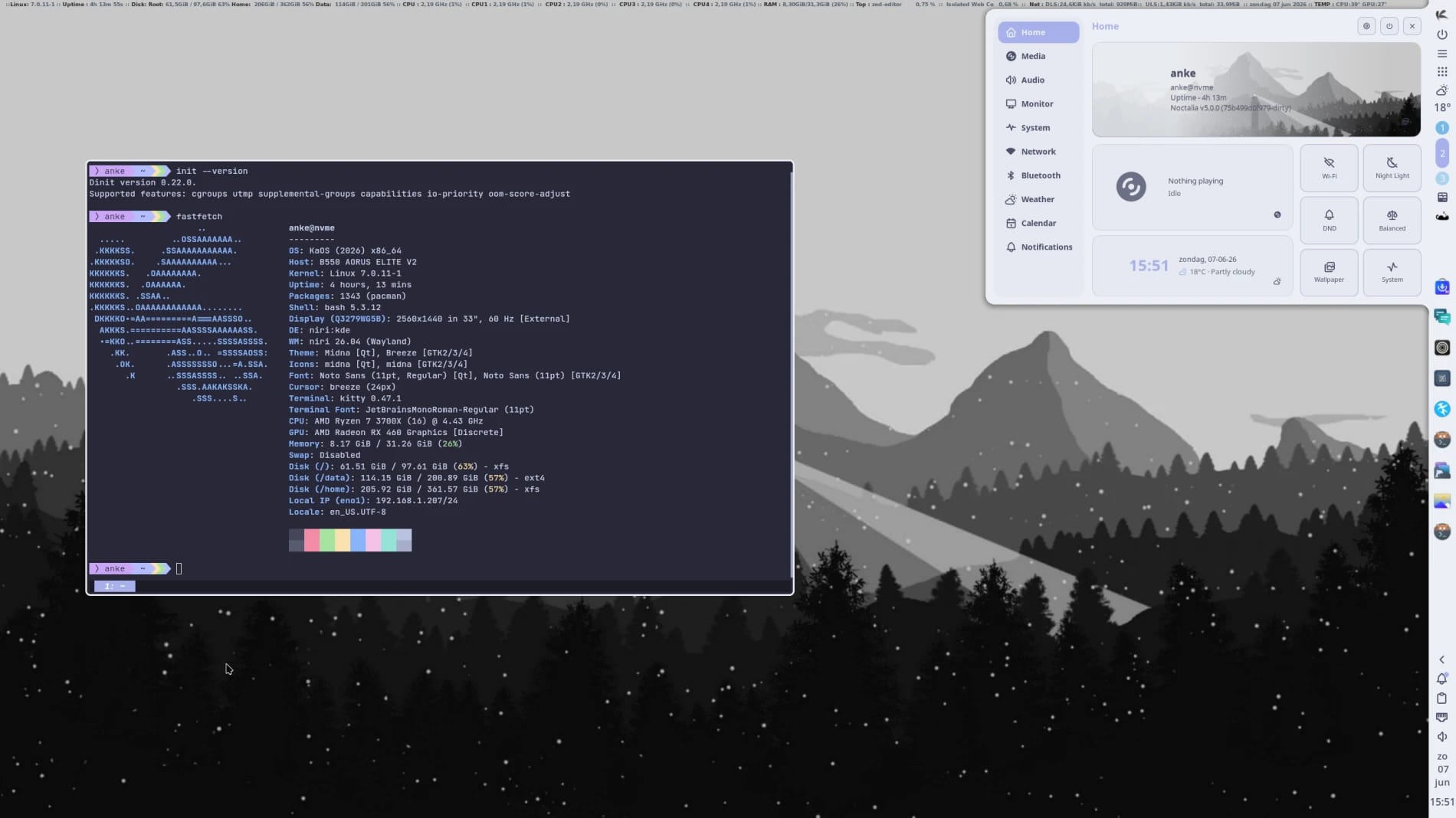
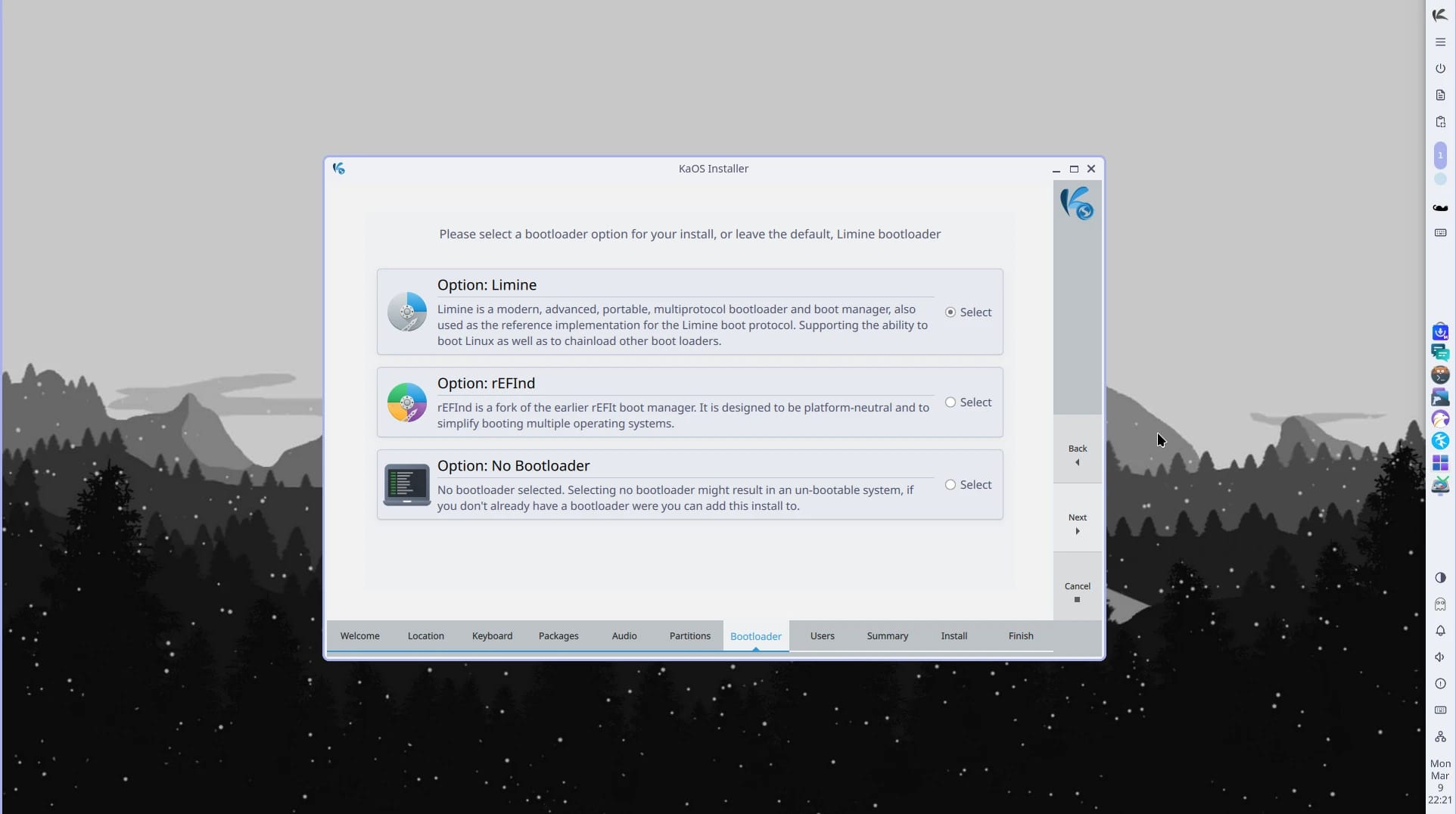
You know what else is everywhere? systemd. Well... almost. KaOS has decided to distance itself from systemd and opted for dinit instead.
🧠 What We’re Thinking About
ProtonMail is a solid Gmail alternative for privacy-conscious users, but the absence of canned responses is still a daily pain point for me.
🧮 Linux Tips, Tutorials, and Learnings
Man pages are famously dense, but they're also the most accurate and complete documentation Linux has.
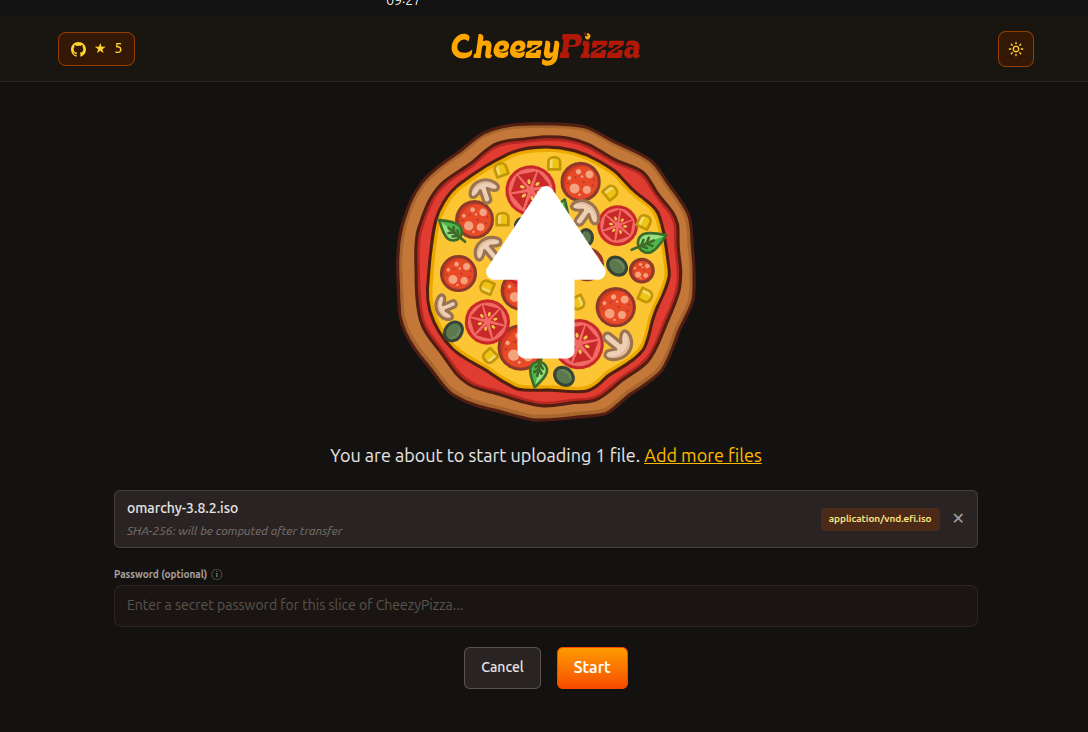
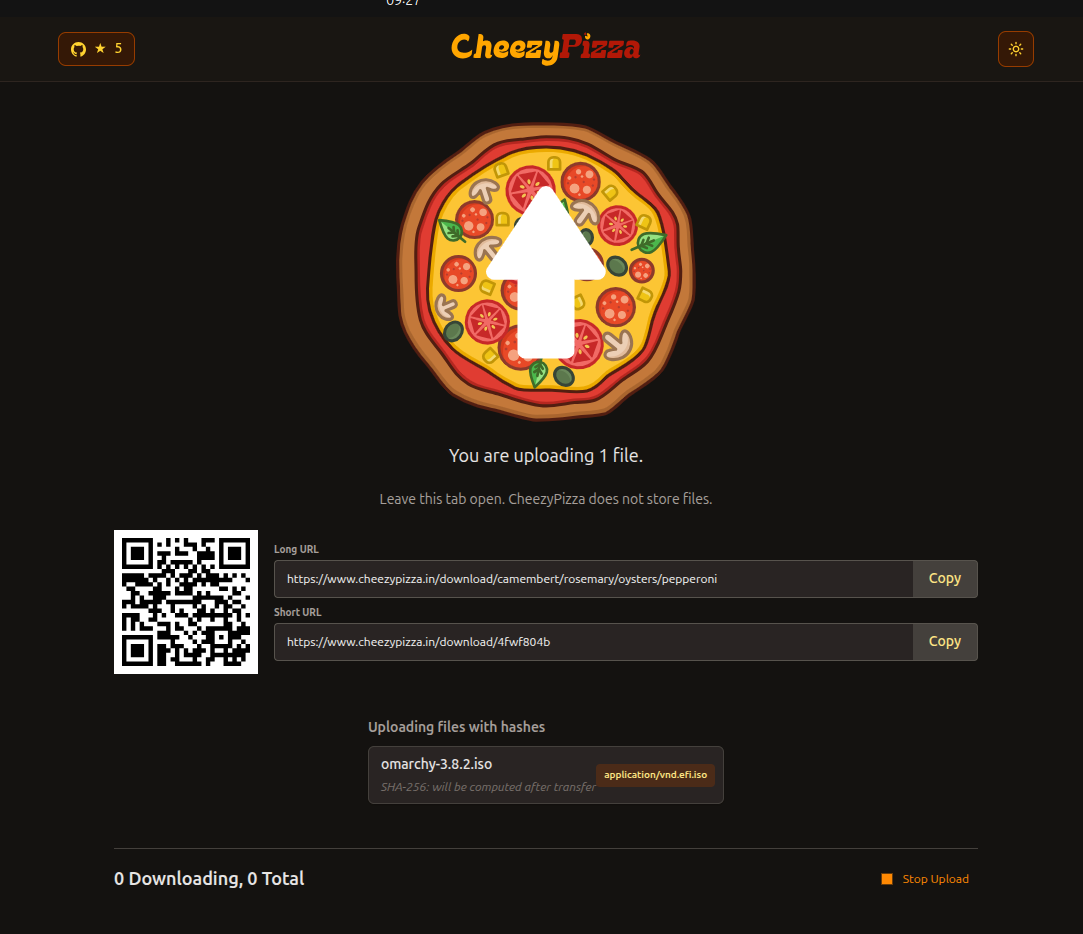
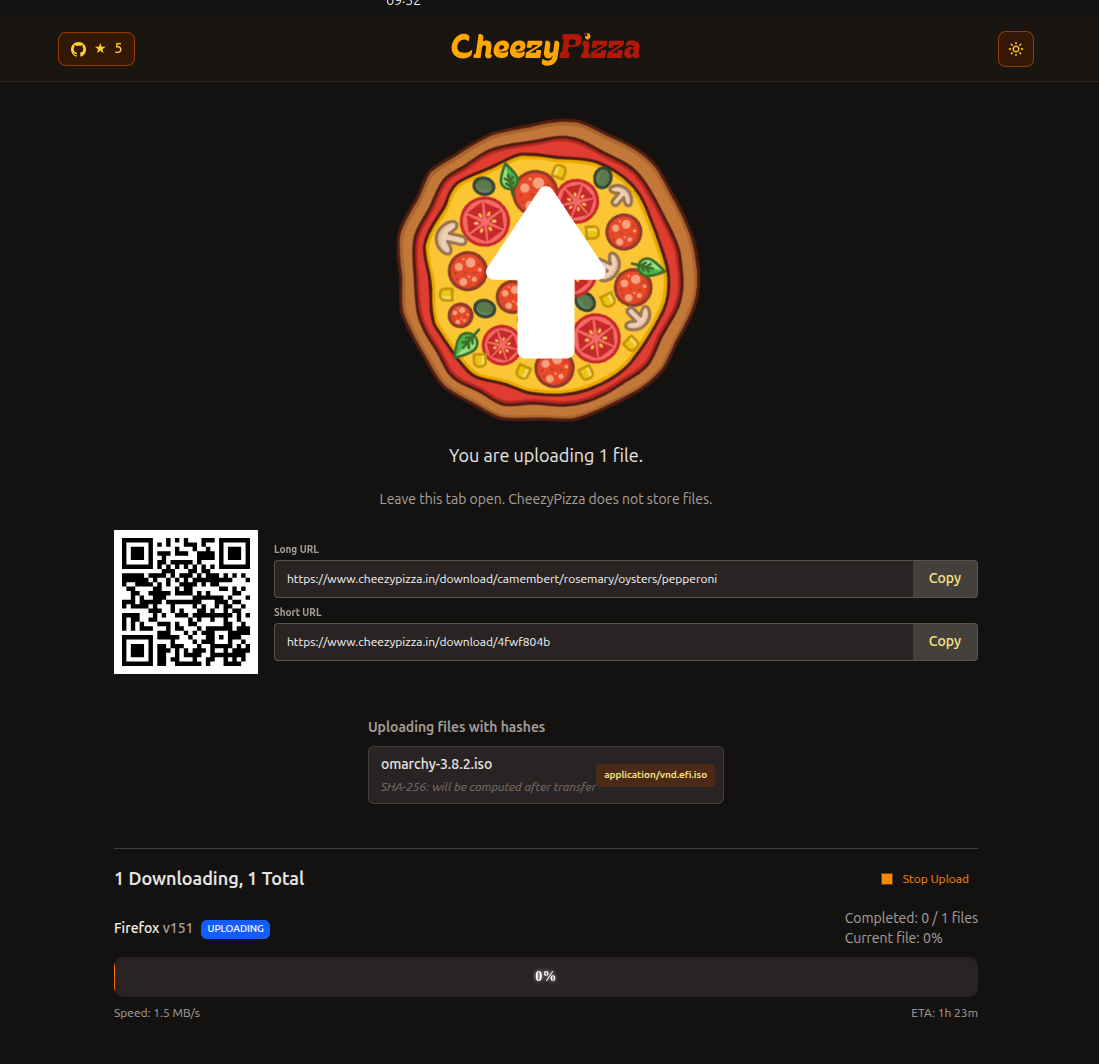
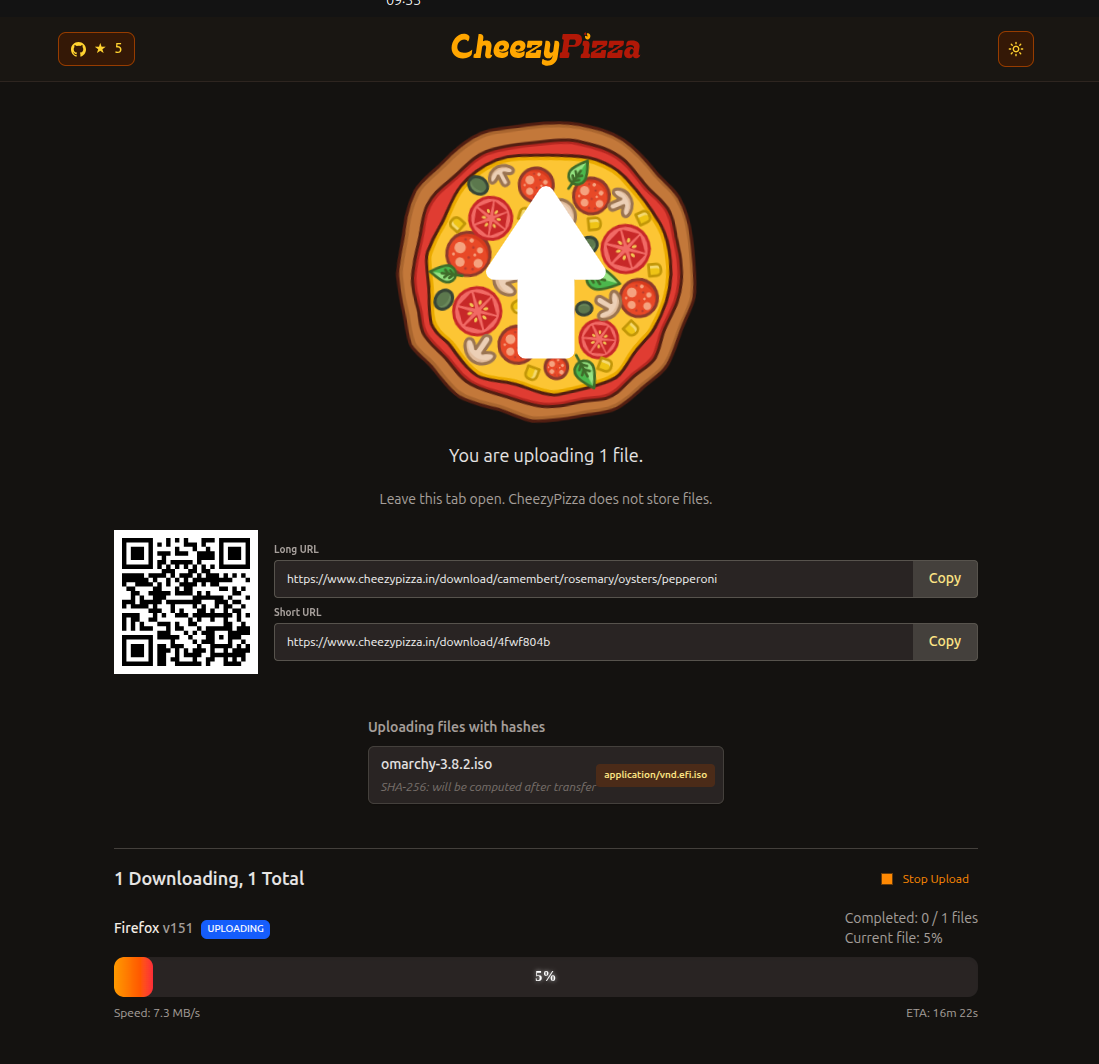
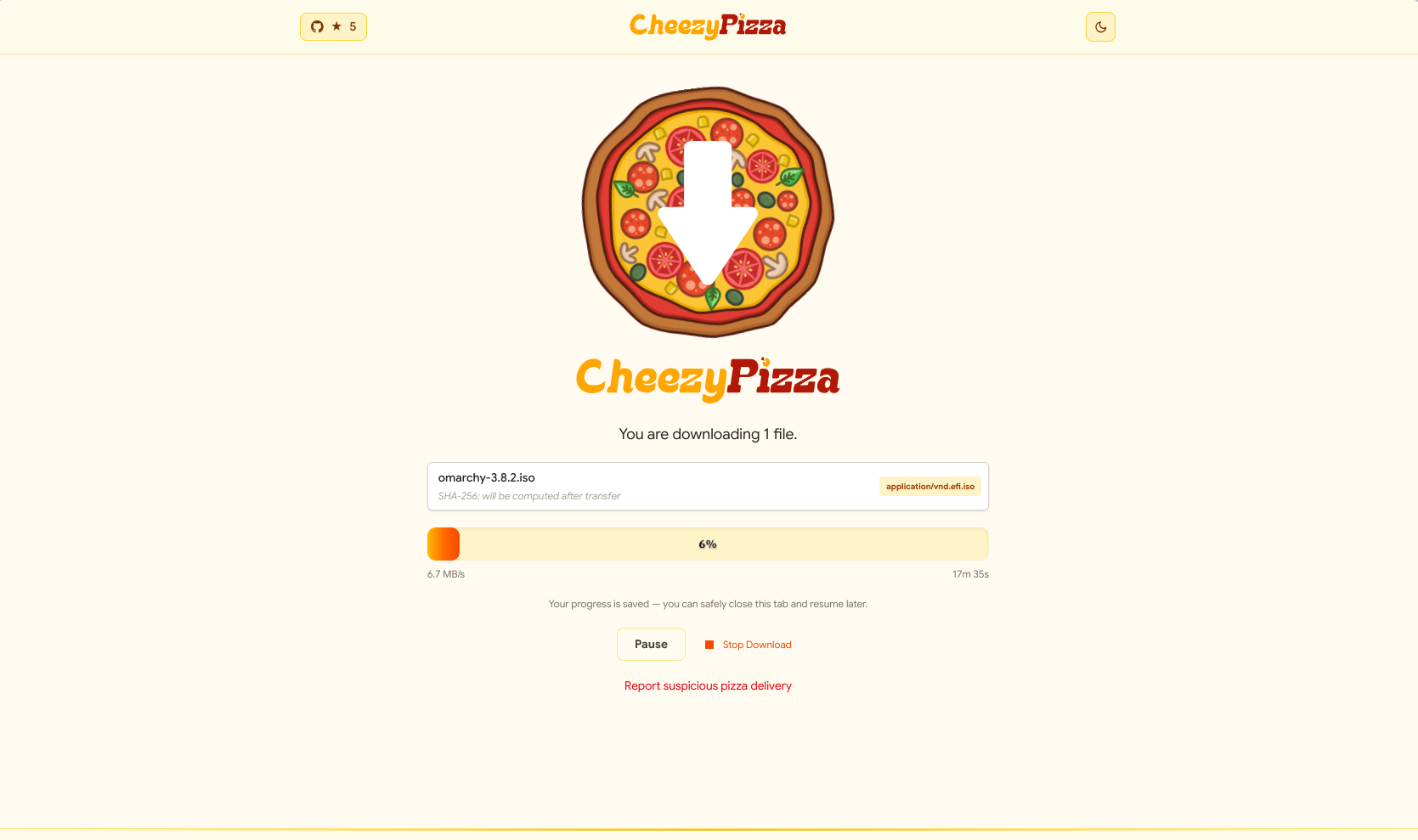
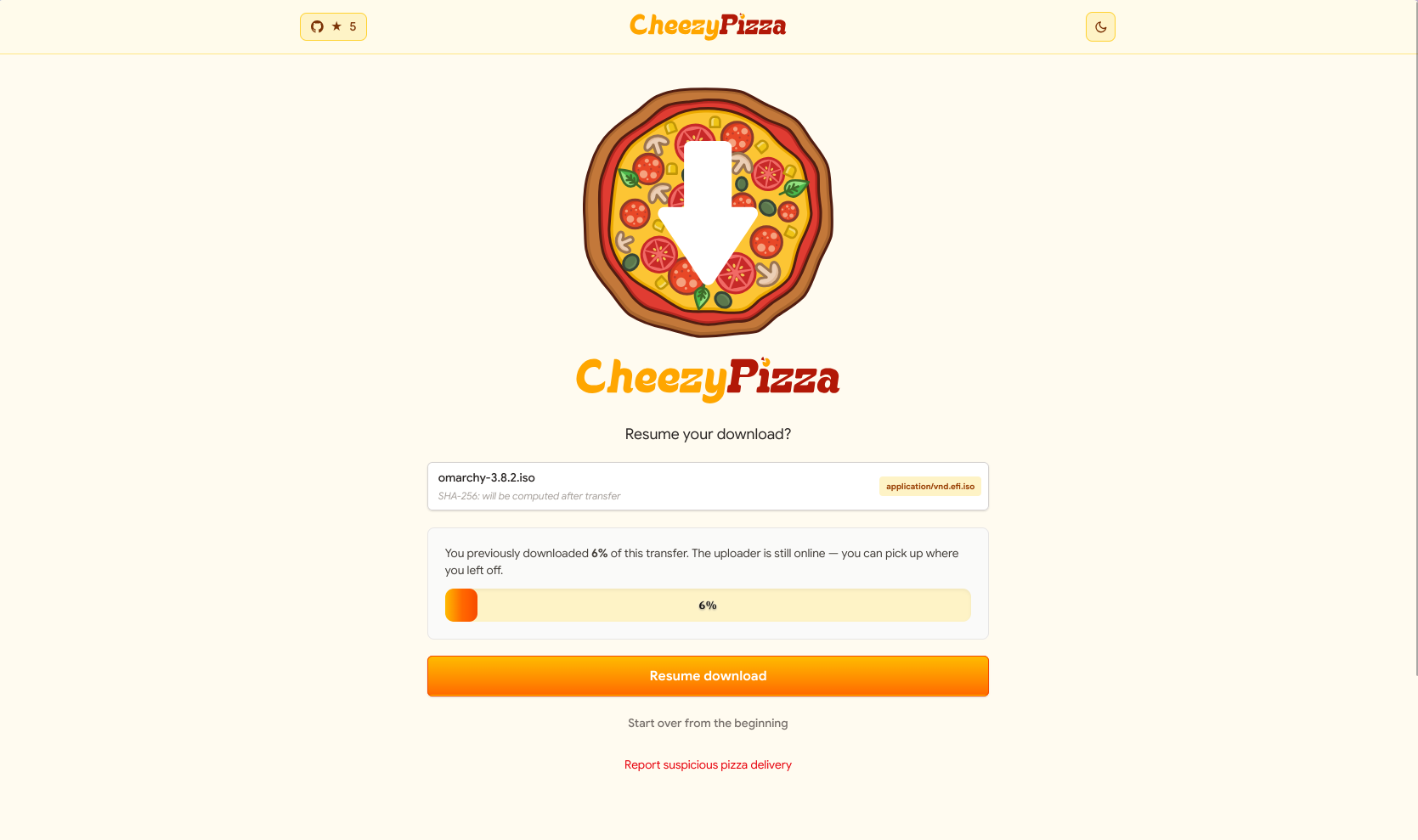
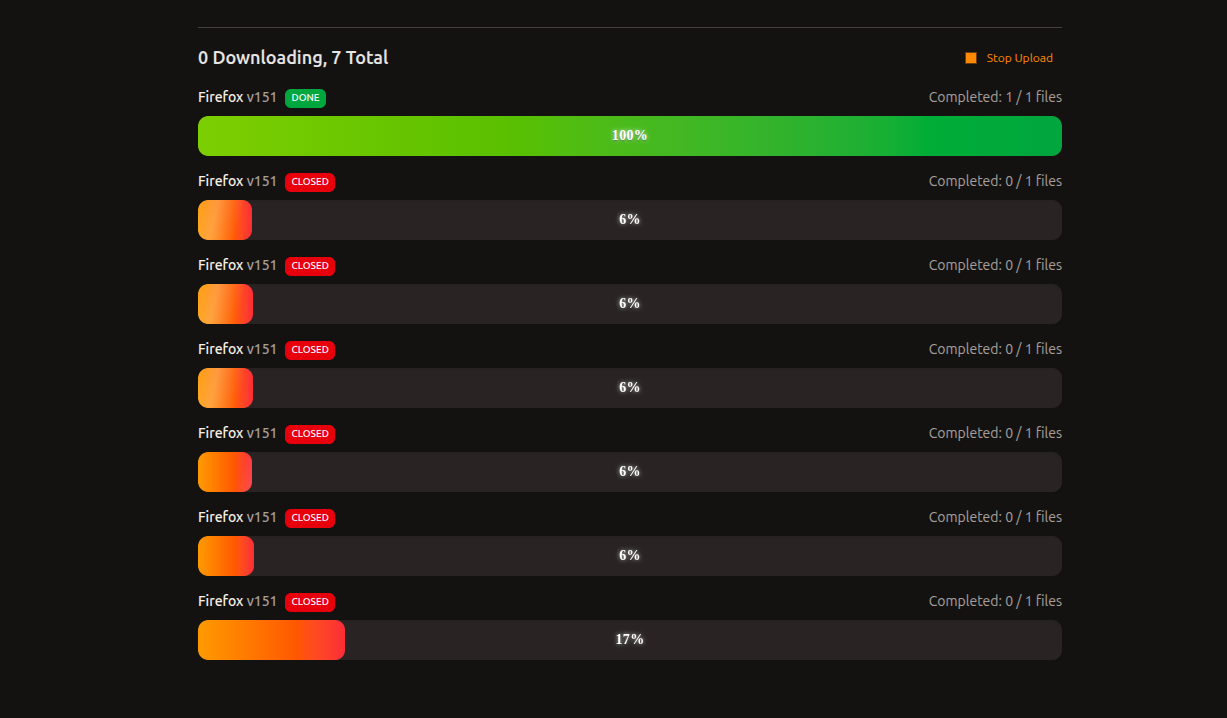
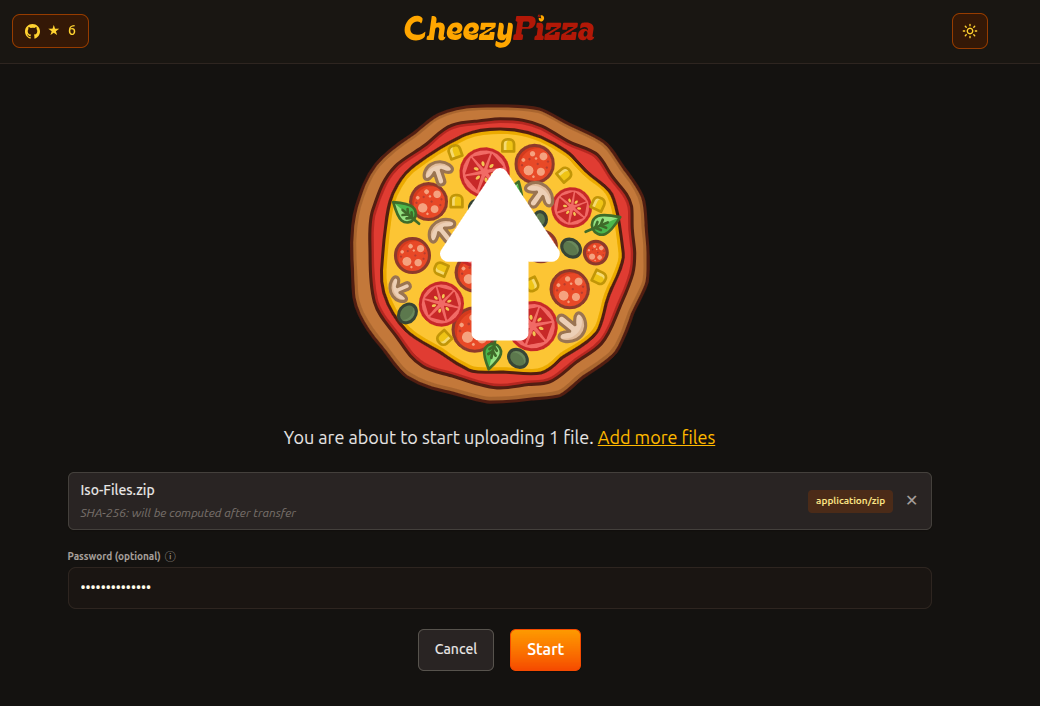
Need to send a large file without uploading it to someone else's server first? CheezyPizza does it browser to browser over WebRTC, with no account, no size cap, and no middleman.
Not open source software but Melia is a new Linux desktop email client that takes privacy seriously in ways most clients don't bother with. Tracking pixels are neutralized, incoming emails are verified against SPF, DKIM, and DMARC, and senders whose display names don't match their addresses get flagged automatically.
If you find Linux Mint running slowly, try disabling animations and window effects. It may improve the performance a yiny bit and tiny bits help when you are struggling with performance.
On the contrary, if you have decent hardware, you can add eye candy to Linux Mint by adding more desktop effects.
👷 AI, Homelab and Hardware Corner
Bambu Lab has been on a path to vendor lock-in, and even after outcry from the community over some of its recent moves, they don't seem to be learning anything.
Luckily, the open source community knows how to respond to such predatory behavior.
✨ Apps and Projects Highlights
Dank Linux is in the Arch+Hyprland zone. It gives you a preconfigured Hyprland to enjoy.
AliasVault can be a refuge from your escape from Bitwarden, seeing how they have been pulling off some major moves quietly.
📽️ Videos for You
If you use top to monitor processes in Linux, you ought to know some of its lesser-known commands.
💡 Quick Handy Tip
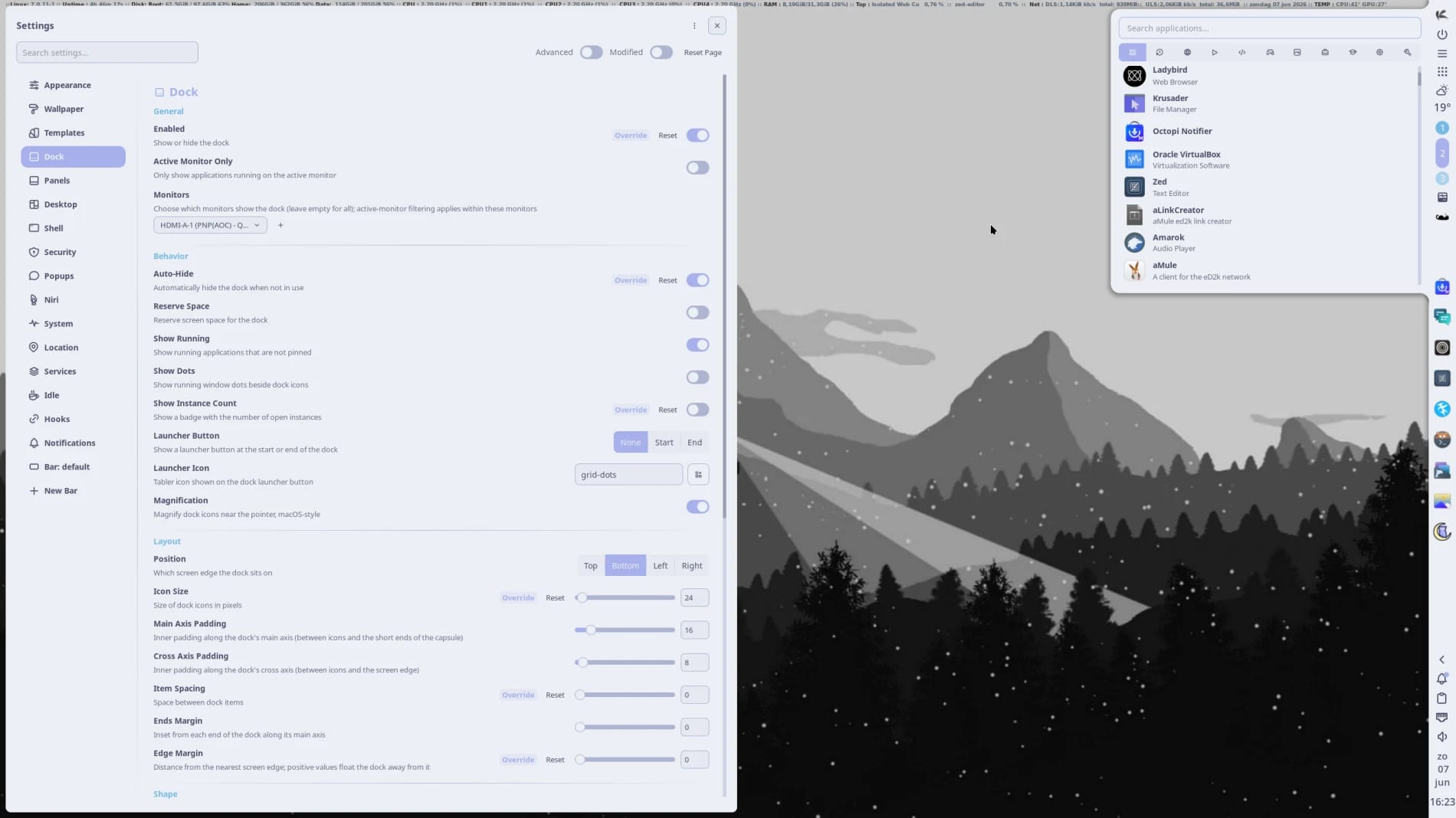
If you are on a GNOME setup, then you can enable certain user interface settings on the Resources app to display important usage and hardware-related details in the sidebar at all times.
Go into the "Preferences" menu via the hamburger button (looks like three lines), then under the "General" tab, look for these options and enable them:
- Show Usage Details in Sidebar
- Show Device Descriptions in Sidebar
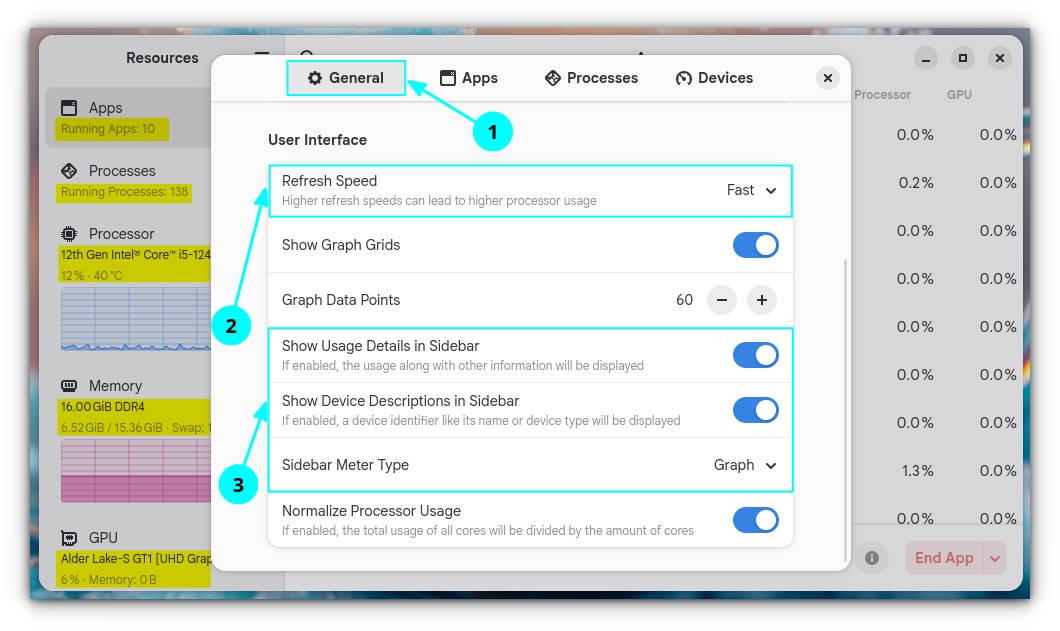
Suggested Read 📖: Mission Center vs. Resources
🎋 Fun in the FOSSverse
There have been many instances of the open source community striking back at projects that locked down. We have a puzzle that will test your knowledge of such occurrences.
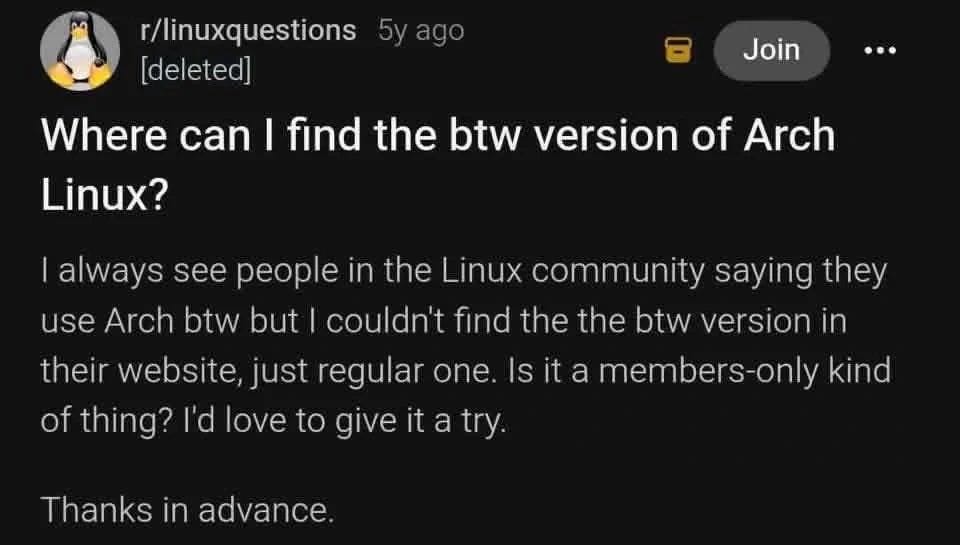
Can you help this Arch user? 🤣
🗓️ Tech Trivia: On June 7, 1954, Alan Turing, the mathematician who conceived the theoretical blueprint for modern computers and helped crack Enigma cipher at Bletchley Park, reportedly took his own life at age 41.
His work helped shorten World War II and laid the foundation for every computer running today.
🧑🤝🧑 From the Community: A newcomer is asking which web browsers his fellow FOSSers are using. Care to contribute?
from It's FOSS https://ift.tt/4krCotA
via IFTTT